on
The news lately has covered several instances of “ghosts” being used to spy on private citizens. For example, a recent article by the Daily Caller covers how Carter Page was spied on by the FBI. You may not hold a position of prominence but that doesn’t mean you aren’t still being spied on by the government or criminals.
There are many ways to protect yourself from the prowling eyes of “Big Brother” and others who make a living following your every cyber move, but do keep in mind that nothing is 100% fool-proof. You have to assume that scammers, spammers, and others spend their days and nights finding ways to make your online experience vulnerable and under constant threat. That doesn’t mean you should succumb or act recklessly online, however.
1. Cover-up
Let’s get started by doing something to cover your computer’s camera since it can be hacked and your camera turned on to record you without your knowledge. If you never use your camera – but a piece of electrical tape over it and you are done.
If, however, you routinely participate in video calls or conferencing then you will want to use something removable. This could be as simple as a couple of stacked post-it notes. I have an auxiliary speaker that clips onto my laptop and can be placed to cover my camera. In the past, I have also used an oversized binder clip.
Keep in mind that covering the camera does NOT shut off your microphone, and if someone is tracking you they will still be able to hear what you are saying.
2. Change your passwords
This should go without saying, but there are still people who are using “password” as their password for everything. Experts recommend having a unique password for every site and they say that it is a good idea to change your password to complex ones (a mixture of letters, numbers and special characters) and to change them every few months. Your security is only as good as your weakest password.
3. Use a VPN
A VPN, or virtual private network, is software that secures and privatizes data across the Internet by building an “encrypted tunnel.” When you access the Internet, your data passes through this tunnel which protects it from anyone who tries to intercept it. A VPN encrypts everything: your email, your web browsing history, your IMs, your VOIP, everything. Another benefit of using a VPN is that even if your data is intercepted, your identity is protected, since a VPN masks your IP address.
4. Pay attention to your privacy settings and updates to privacy options.
Look through your current online privacy settings, and set them according to your comfort level. Remember that when a company alters their privacy settings and security contracts, your previous settings are often not retained. Stay up to date and edit your settings. You may even wish to set a reminder on your phone for a monthly password change and check-up. The documentary, Terms and Conditions May Apply, takes a critical look at the ever-changing User Agreement policies.
5. Protect your Smart Phone
We use our Smart Phones just about everything these days and protecting our data is important for our privacy. If you haven’t already installed the app called Signal you need to do so, and to convince the people you message with the most often to do so as well as it only works if everyone being sent the message has the app. It doesn’t change how your texts or calls are made, it only encrypts them.

Signal is safer and more secure than most messengers because of a process called “end-to-end encryption.” This works by encoding a sender’s message in such a way that only the intended receiver’s device can unlock it.
Neither Signal, nor your phone company, nor the government can read your messages. That’s why it’s remained popular with journalists, government officials, and anyone else who deals with classified materials.
And Signal isn’t only for mobile phones, it also works on desktops, laptops and tablets too.
6. Avoid open unknown Wi-Fi networks
This is true no matter what type of device you are using. 99.99% of the time these are malicious site intent on stealing your data. Be especially leery of any open networks even if you recognize the name in places such as airports, train stations or anywhere there are large groups of people unless you see “free WI-Fi” with that specific name advertised in that location.
7. Use Virus & Malware protection
Many hackers use malware to get their hands on your personal information. This software allows them to delete and steal information from your computer. You should never use a computer that does not have anti-virus protection. Most services are affordable, and they are well worth it in the long run.
You should also understand that your phone and tablet aren’t safe either. Hackers can easily get into these devices as well; therefore, you should be sure to download an app that offers the same kind of protection. Many times a subscription comes with a mobile version as part of the bundle.
8. Turn off locations
It is a good idea to turn off your location when using your digital device. Also, if you are on a website and a box pops up after if you want to share your location, you should always click, “no.” If your location is on or shared, just about anyone can find you, including hackers.
Make sure you turn off the metadata that gives locations in your images, as well as that information, could be used to track your whereabouts or to confirm a time/location stamp from other spying software.
9. Don’t click!
Finally, be very cautious about clicking on unknown or unsecured links.
Phishing is one of the most common ways that scam artists try to get a hold of your personal information. They often send emails that appear to be from reputable companies, or even from people that you know. They will attach a link or an attachment to the email that contains malware or other viruses. When you click on the link, they can gain access to your personal information. If you get an email, beware of the attachments and the links, even if you think that you know who the email is from.
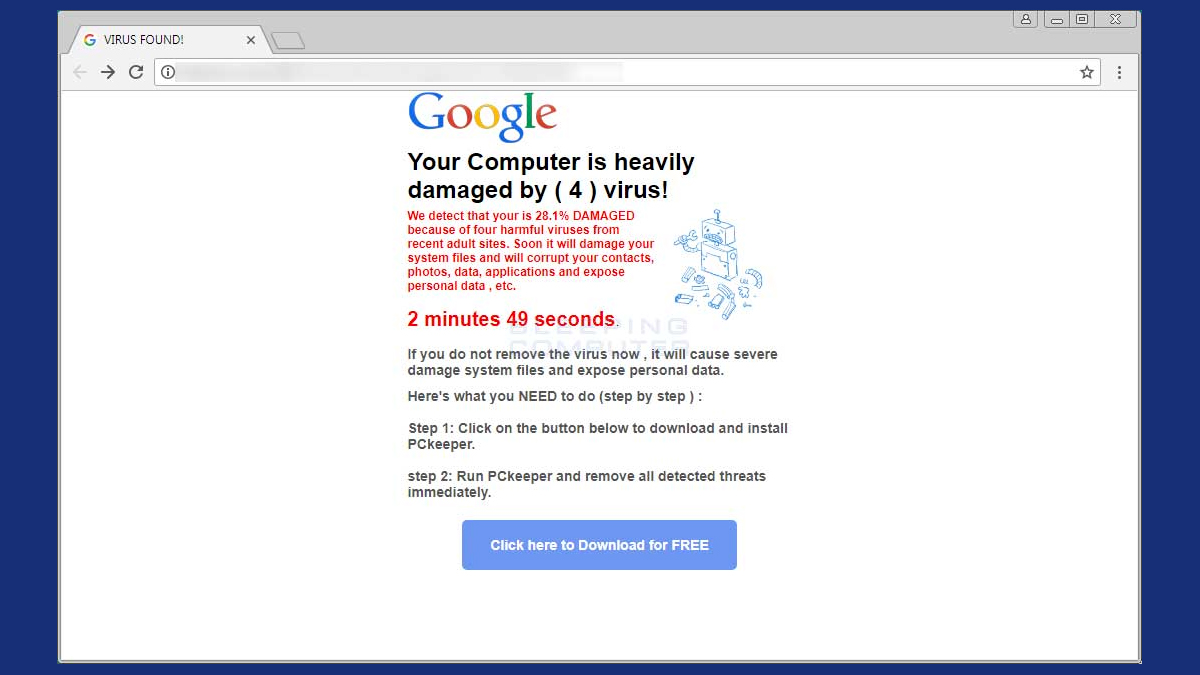
“Big Brother” has been known to use the exact same tactics as scammers that install malware on your device. They can use it to turn on your camera, listen in and to take data without your knowledge or consent.
Studies have shown that people are 33% more likely to open a risky link from an unknown source from their phones than they are form a desktop or laptop. So far, no one seems to know why having a hand held device causes more risky behavior. So be extra careful when using your phone or tablet.
When you are online, you need to make sure that the site that you are using is secure. If it isn’t, there is a good chance that there is a hacker on the other end just waiting to get their hands on your personal information.
Look for the small padlock in front of the website that you are using. If the padlock is closed, it means that the site is secure. If you want to double-check, simply click on the padlock, and the name of the company will come up. It will also let you know if the site is secure.
Get access to premium content and more!